A Verifiable Credential is a digitally signed credential that lets a person prove a claim to someone else in a way that can be cryptographically checked - wikipedia ![]()
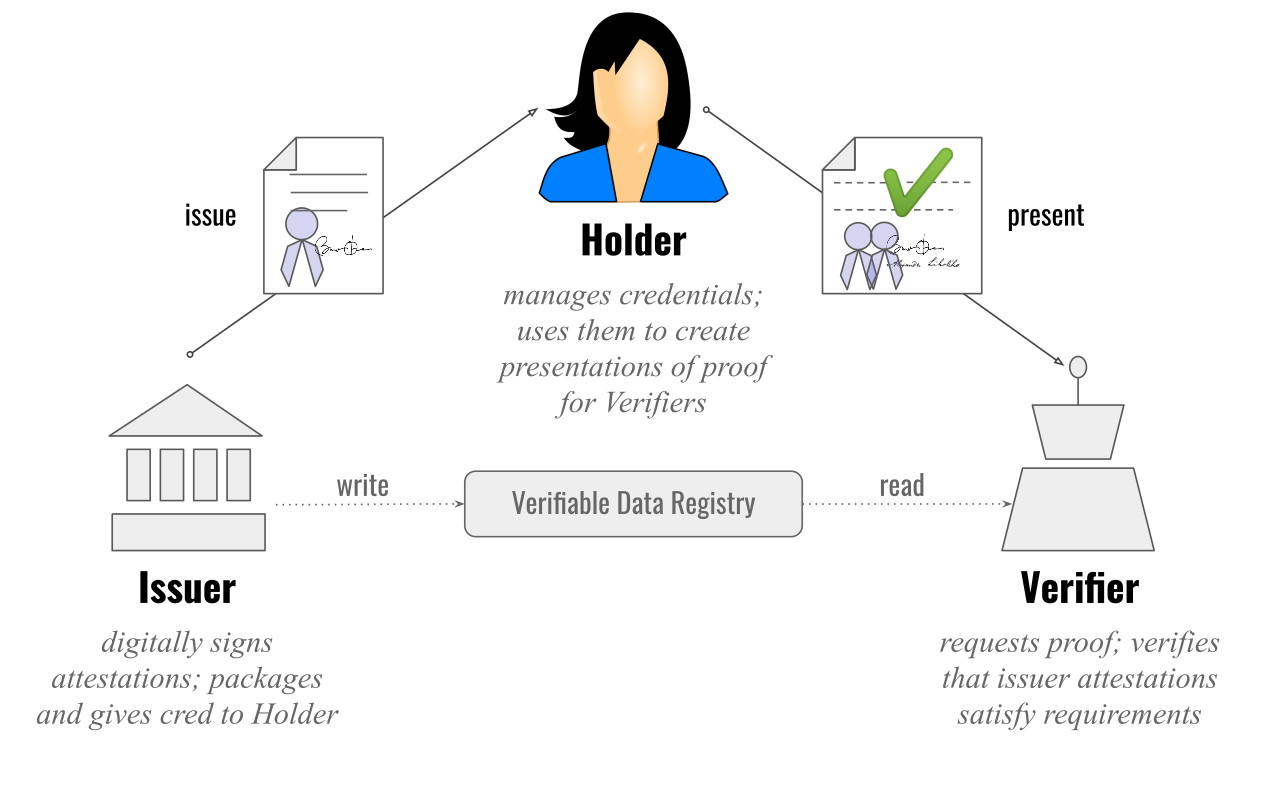
The holder of a verifiable credential operates in a triangle of trust, mediating between issuer and verifier. The issuer and holder trust each other, the holder trusts the verifier, and the verifier trusts the issuer. Any role in the triangle can be played by a person, an institution, or an IoT device - wikipedia ![]()
It is the digital analogue of a paper credential such as a driving licence, a student card, or a membership certificate, except that the verifier can validate who issued it, whether it has been tampered with, and whether it is still valid, without needing to phone the issuer every time.
In the W3C model, a Verifiable Credential is issued by an issuer, held by a holder (usually in a wallet app), and checked by a verifier. The credential contains claims about the holder (the “credential subject”), and it can be presented as a verifiable presentation that the verifier can validate cryptographically}.
A practical example is a university degree credential. A university issues a digital credential stating "David Bovill has been awarded a BA in Philosophy,” and you store it on your phone. When applying for a job, you can present the credential to an employer’s hiring system, which verifies the issuer signature and validity rather than relying on a scanned PDF or a phone call to the registrar.
Another everyday example is age verification. Instead of showing a full identity document (name, address, date of birth), you present a credential-derived proof that only answers the policy question, such as “over 18” or “over 21.” This reduces unnecessary disclosure and makes “show me you qualify” more private than “show me who you are,” especially when paired with selective disclosure or zero-knowledge proof techniques.
A third example is employment and access control. An employer issues an employee credential (role, department, access permissions, training completion). When entering a building or accessing an internal tool, you present a proof that you hold an active employee credential with the required role, without exposing irrelevant HR data. This can also support rapid revocation when someone leaves, because the verifier checks freshness and status rather than trusting an old screenshot.
A fourth example is regulated or high-assurance digital identity wallets, such as the EU Digital Identity Wallet work. In that ecosystem, a wallet may store identity data and attribute attestations (for example, qualification or authorisation attributes) and support interoperable presentation in specific public and private sector journeys.
At the plumbing level, there are emerging interoperability protocols for issuing credentials into wallets and requesting them from holders. One widely referenced approach is OpenID for Verifiable Credential Issuance, which defines an OAuth-style API for issuing credentials in multiple formats.
The point of verifiable credentials is not “put your whole life on a blockchain.” It is to make trust portable: credentials can be held by the person, verified by many parties, and expressed as minimal, checkable claims that support safer participation in digital services and governance without turning every interaction into a privacy sacrifice.
# See